Android MediaProjection Bug Lets Attackers Record Audio and Screen

Since Android 5.0 Lollipop, there exists a new MediaProjection API that allows apps to record videos and take screenshots of other apps. The feature brought screen-capturing and screen-sharing capabilities to Lollipop with a new 'createVirtualDisplay()' method that allowed apps "to capture the contents of the main screen (the default brandish) into a Surface object, which your app can so send across the network". While the service was technically present in Android from the starting time, apps originally needed root access to use it; a requirement that was washed away with from Android 5.0.
However, while apps require a special permission to use the MediaProjection API, no such permission is needed to use the platform features, which is something that now seems to accept rendered about 77.five% of Android devices worldwide vulnerable to an attack that reportedly exploits this loophole to surreptitiously capture users' screen and tape organization audio. Affected Android versions include Lollipop (both 5.0 and 5.one), Marshmallow and Nougat. Google has patched up the vulnerability in Android Oreo.
In the affected versions of Android, apps don't need whatever specific permission to utilise the MediaProjection service, and tin, instead, request access to it through a SystemUI popup to inform the user about its intent to capture screenshots or record system audio. The trouble, however, is that apps tin detect when this SystemUI alarm is about to popular up, allowing rogue apps to superimpose a fake text on peak of the SystemUI warning, thereby fooling unsuspecting users into allowing their screens or audio to exist recorded without knowing what they are agreeing to. Unfortunately, affected Android versions are unable to detect partially-hidden SystemUI pop-ups, leaving users potentially vulnerable to serious privacy breaches.
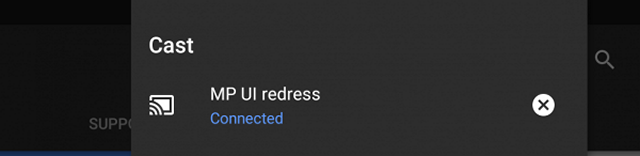
Known equally 'Tap-jacking' in security parlance, this serious design flaw in Android was discovered last winter by security researchers from MWR Labs. According to the team behind the discovery, cyber-criminals can "trivially bypass this mechanism past using tapjacking this pop-upwards using publicly known methods to grant their applications the ability to capture the user's screen". Thankfully, though, users will receive a heads-up whenever whatsoever app tries to access the MediaProjection service to tape audio or screenshots, so exercise watch out for the screencast icon on the notification bar (as seen above) if y'all suspect whatever rogue activity on your device.
Source: https://beebom.com/android-mediaprojection-bug-record-audio-screen/
Posted by: daleycoloody.blogspot.com


0 Response to "Android MediaProjection Bug Lets Attackers Record Audio and Screen"
Post a Comment